Ransomware Recovery: What Happens After an Attack
Most cybersecurity conversations in healthcare focus on prevention. Firewalls, training, MFA, patching — all of it aimed at keeping attackers out. That’s the right instinct. But prevention alone isn’t a complete strategy, because no defense is perfect.
What happens when an attack gets through? What does the recovery process actually look like — and how long does it take?
These are questions every healthcare organization should be able to answer before they’re in the middle of a crisis.
The First Hours: Contain and Assess
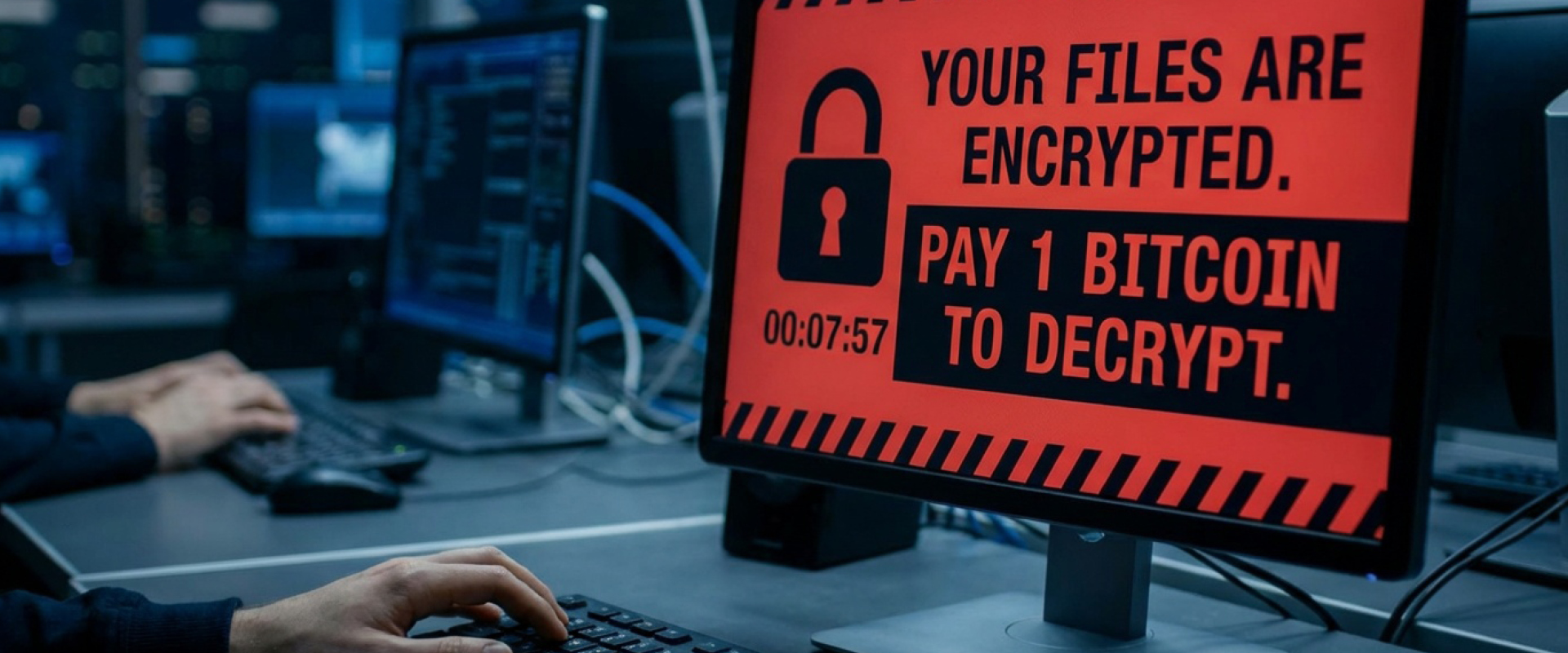
When ransomware activates, speed is critical. The malware’s goal is to spread — encrypting files across as many systems as possible before anyone notices. The first priority is containment: isolating infected systems from the network to limit the damage.
This is where a tested incident response plan pays off. Organizations that have documented procedures and practiced them move significantly faster in the first critical hours than those improvising in real time. Every minute of delay is potentially more data encrypted, more systems affected, more downtime ahead.
Once containment is underway, the assessment begins. What systems were hit? What data was accessed or exfiltrated? When did the attacker first enter the environment? (Often, attackers have been inside a network for weeks before deploying ransomware — your logs may tell a story you weren’t aware of.)
The Decision No One Wants to Make
At some point, most organizations face the question of whether to pay the ransom. It’s a decision with no good answers.
Paying doesn’t guarantee you’ll get your data back — or that the attacker won’t strike again. It may also create legal complications, particularly if the attacker is on a sanctions list. Law enforcement agencies generally advise against payment.
The organizations with the most leverage in this moment are the ones with clean, tested backups that aren’t connected to the compromised environment. If you can restore from backup, the calculus changes entirely.
Recovery: Slower Than You Think
Even with good backups, full recovery from a ransomware attack is rarely quick. Restoring systems takes time. Validating that the attacker is no longer present takes time. Rebuilding trust with staff, patients, and regulators takes even longer.
Healthcare organizations that have been through it describe the process in weeks and months, not days. Clinical operations are disrupted. Staff fall back on paper processes. Patient care can be affected in ways that are difficult to quantify.
The organizations that recover fastest share a few things in common: they had current, tested backups; they had a documented response plan; and they had a trusted IT partner who could work alongside them through the process — not just hand them a report.
What You Can Do Now
You don’t have to wait for an attack to get prepared:
- Test your backups. Not just whether they exist — whether you can actually restore from them.
- Document your incident response plan. Who gets called? In what order? Who has authority to make decisions?
- Know your vendor relationships. Which partners need to be notified immediately? Who can help with forensics and recovery?
- Review your cyber insurance policy. Understand what’s covered, what the claims process looks like, and what documentation you’ll need.
Ransomware recovery isn’t a topic anyone wants to think about. But the healthcare organizations that fare best aren’t the ones who were never attacked — they’re the ones who were ready when it happened.
Contact us to learn more about how Abacus can support your organization’s efforts to be resilient to cyberattacks.